2026-02-03, 14:50–15:40, B.1.0.14
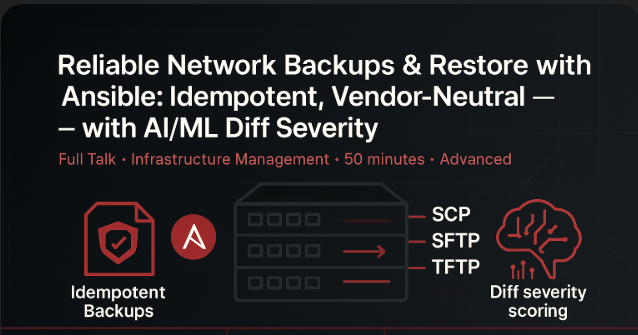
In network automation, reliable backups are critical but often overlooked. This session explores how to design a consistent, vendor-neutral backup and restore workflow using Ansible.
Backups that “usually work” aren’t good enough. This talk presents a battle-tested, backup/restore workflow for Cisco IOS/IOS-XR/NX-OS using Ansible and Validated Content. We’ll show how to pick the right transfer method (SCP/SFTP/TFTP), enable and secure internal file servers, and make tasks idempotent across vendors. We’ll also cover selecting device-native paths (bootflash:/, disk0:, /misc/config) to avoid path pitfalls.
We will also go through a lightweight, offline rules + ML approach that scores the severity of configuration diffs (e.g., VLAN/ACL/BGP/interface changes) to prioritize reviews and automate safe rollbacks. Live demos include copying configs, verifying hashes, ranking diff severity, and controlled restores.
Modern network automation needs backups that are deterministic, auditable, and work without Internet access. This session walks through:
Patterns & pitfalls: Use absolute on-device paths (e.g., flash:/configs/backup.cfg, bootflash:/...) and do not rely on shell shortcuts like ~ (most network OSes don’t expand them). Choose the right transfer method (SFTP vs SCP) and prefer secure, internal file servers.
Idempotent backups: canonicalizing configs, hashing (SHA-256), and writing only on change.
Vendor neutrality: switching cleanly across IOS / IOS-XR / NX-OS with a single role interface.
Device-native storage: choosing bootflash:/, disk0:, /misc/config and verifying available space.
Restore safety: stage → replace/merge → post-verify via hash/lines match.
Diff severity scoring: simple feature extraction + rules (optional scikit-learn) to rank risk and trigger rollbacks.
Principal Engineer, Ansible Networking. Works on networking content engineering, Ansible Automation Platform collections, and AI enablement in network automation.